TL;DR: ITIL change management frameworks require risk assessment before production changes, but most Change Advisory Boards approve releases based on developer assurances and cursory checklists -- with zero objective security evidence. Automated penetration testing fills this gap by providing a "security certificate" for each change: a documented, timestamped pentest result proving the change was tested for exploitable vulnerabilities before it reached production. This article explains how to integrate pentesting into ITIL change workflows, build security certification into change policy, and connect the process to ITSM tools like ServiceNow and Jira Service Management.
Every mature IT organization has a change management process. There is a Change Advisory Board. There are change request forms. There are approval workflows. And in the vast majority of organizations, changes are approved for production deployment without a single piece of objective evidence that the change does not introduce exploitable security vulnerabilities.
This is not a niche problem. It is the default state of change management across industries. The ITIL framework prescribes risk assessment as a core component of change evaluation, but the framework does not specify how security risk should be assessed. So most organizations fill the gap with subjective assessments: the developer says the change is safe, the QA team confirms functional correctness, and the change manager checks a box. No one tests whether the change can be exploited by an attacker.
The Change Management Security Gap
To understand the gap, walk through a typical change management workflow.
A development team completes a new feature or infrastructure modification. They submit a change request through the organization's ITSM platform. The change request includes a description of the change, its business justification, a rollback plan, and a risk assessment. The risk assessment typically consists of a categorical rating -- low, medium, or high -- based on the scope of the change and the criticality of the affected system.
The Change Advisory Board reviews the request. Members may include IT operations, development leads, business stakeholders, and sometimes a security representative. They evaluate the change based on the information provided, ask clarifying questions, and approve, defer, or reject the change.
Here is the problem: the risk assessment is almost entirely subjective. The developer rates their own change as "low risk" because they understand what the code does and believe it is secure. The QA team confirms that the feature works as designed. But no one has tested whether the change introduces an authentication bypass, exposes a new API endpoint without proper authorization, creates a path traversal vulnerability in a file upload handler, or introduces a server-side request forgery through a new integration.
The CAB approves the change based on trust, not evidence. And for the 99% of changes that do not introduce exploitable vulnerabilities, this works fine. For the 1% that do, the organization discovers the vulnerability the hard way -- through a security incident, a customer-reported bug, or a pentest months later.
Where Pentesting Fits in ITIL Change Management
ITIL 4 defines change enablement as a practice that "maximizes the number of successful changes by ensuring that risks have been properly assessed." The framework identifies three types of changes:
Standard changes are pre-authorized, low-risk changes that follow a repeatable procedure and do not require CAB review. Normal changes require assessment and authorization through the standard workflow -- new features, infrastructure modifications, integration deployments. Emergency changes are expedited due to urgent business need and documented retroactively.
Penetration testing maps most naturally to normal changes, particularly those classified as medium or high risk. The pentest provides the objective security evidence that the risk assessment currently lacks. Instead of the developer self-certifying that the change is secure, the organization has a documented test result proving that an independent assessment was performed.
For emergency changes, pentesting should be performed retroactively. The change is deployed under expedited approval, and a pentest is triggered against the production environment within 24-48 hours to validate that the emergency change did not introduce exploitable vulnerabilities. This retroactive testing closes the loop on emergency changes that bypassed the normal security gate.
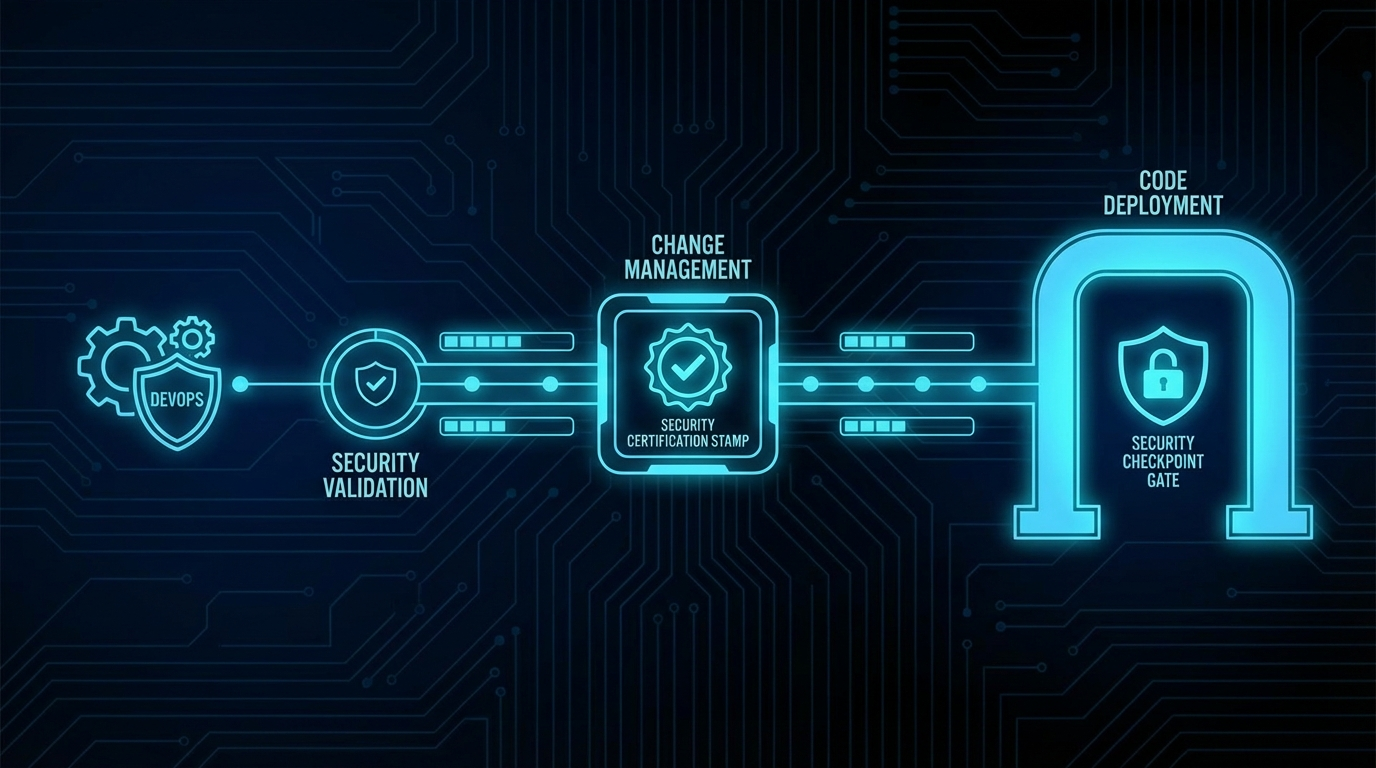
The Security Certificate Concept
Think of penetration testing as producing a "security certificate" for a change -- analogous to how QA testing produces a "quality certificate." Just as QA sign-off certifies that the change functions correctly, the security certificate certifies that the change was tested for exploitable vulnerabilities.
The security certificate is a structured document (or record in your ITSM system) that contains:
- Change ID: The identifier of the change request it certifies
- Test scope: What was tested (specific endpoints, systems, or components affected by the change)
- Test date and duration: When the pentest was performed and how long it ran
- Methodology: What types of testing were performed (web application testing, API testing, network testing, authentication testing, etc.)
- Findings summary: Number and severity of exploitable vulnerabilities discovered
- Critical/High findings detail: Specific description of any exploitable vulnerabilities that would block the change
- Certification status: Pass (no exploitable High or Critical findings), Conditional Pass (Medium findings that require remediation within a defined timeframe), or Fail (exploitable High or Critical findings that must be remediated before deployment)
- Tested by: The platform or team that performed the assessment
- Report link: Full pentest report for detailed review
This certificate is attached to the change request in the ITSM system, providing the CAB with objective security evidence alongside the existing QA results, business justification, and rollback plan. The change manager can make an informed approval decision based on actual security testing rather than subjective risk ratings.
Integration With ServiceNow
ServiceNow is the dominant ITSM platform in enterprise IT, and integrating automated pentesting into ServiceNow change management creates a seamless workflow for change managers.
The integration flow works as follows:
- A change request is created in ServiceNow and moves through the normal approval workflow.
- When the change reaches the "Testing" or "Pre-Implementation" state, the ServiceNow workflow triggers an automated pentest via the ThreatExploit API. The API call includes the change number, the target environment (staging), and the scope of testing based on the systems affected by the change.
- ThreatExploit executes the pentest and posts results back to ServiceNow via a webhook or REST API callback. The results are stored as an attachment or linked record on the change request.
- The security certificate is auto-generated and populated on the change record. If the pentest found no exploitable High or Critical vulnerabilities, the certificate status is "Pass." If exploitable vulnerabilities were found, the status is "Fail" with details.
- The change manager reviews the security certificate as part of the CAB evaluation. Pass certificates support approval. Fail certificates require remediation before the change can proceed.
This integration can be configured as mandatory for specific change categories (high-risk changes, changes to customer-facing systems, changes to systems in compliance scope) or optional for lower-risk changes. The ServiceNow workflow engine handles the routing logic, and the pentest step integrates naturally into the existing change lifecycle states.
Integration With Jira Service Management
Jira Service Management (JSM) supports a similar integration pattern using Jira's automation rules and REST API capabilities. When a change request transitions to a defined status (e.g., "Awaiting Security Review"), a Jira automation rule triggers a webhook to the ThreatExploit API. The pentest results are posted back as custom fields: Certification Status, Findings Count, Critical Findings, and Report Link.
JSM's workflow engine can enforce the security gate by requiring the Certification Status field to be "Pass" or "Conditional Pass" before the change can transition to "Approved" status. This structural enforcement means changes cannot bypass the security gate without an explicit override by an authorized change manager -- and overrides are logged for audit purposes.
Building Pentest Requirements Into Change Policy
Technical integration is only half the equation. The other half is policy -- codifying the requirement for security testing into your organization's change management policy so that it becomes a mandatory step rather than an optional enhancement.
Here is a practical policy framework you can adapt:
Scope: All Normal changes classified as Medium or High risk that affect systems in compliance scope (SOC 2, PCI DSS, HIPAA, ISO 27001) or systems that process, store, or transmit sensitive data.
Requirement: Before a change in scope can be approved for production deployment, an automated penetration test must be performed against the change in a staging or pre-production environment. The test must cover the specific systems and components affected by the change.
Security Certificate: The pentest results must be documented in a Security Certificate attached to the change request. The certificate must include the certification status (Pass, Conditional Pass, or Fail), findings summary, and link to the full report.
Approval criteria:
- Pass: No exploitable Critical or High severity vulnerabilities. Change may be approved.
- Conditional Pass: Medium severity exploitable vulnerabilities identified. Change may be approved with a remediation plan and timeline (not to exceed 30 days). Remediation must be verified by a follow-up pentest.
- Fail: Critical or High severity exploitable vulnerabilities identified. Change must not be approved until vulnerabilities are remediated and a retest confirms a Pass or Conditional Pass certification.
Emergency changes: Security testing is not required before emergency deployment but must be performed retroactively within 48 hours. If the retroactive test identifies exploitable vulnerabilities, a follow-up change request for remediation must be submitted as a Priority 1 Normal change.
Exceptions: Exceptions to the security testing requirement must be approved by the CISO or designee and documented on the change request with a risk acceptance justification.
This policy framework gives change managers clear, enforceable criteria. It eliminates the ambiguity of subjective risk assessment for security concerns and provides a documented decision trail for auditors.
Reducing CAB Friction With Automated Reports
One legitimate concern about adding pentesting to change management is that it will slow down the approval process. CAB meetings are already time-constrained, and adding another review artifact could create friction and delays.
Automated pentesting and reporting addresses this concern directly. The pentest runs in the background after the change is deployed to staging -- it does not require manual scheduling, scoping, or coordination. Results are posted automatically to the change record. The security certificate provides a clear, one-line verdict: Pass, Conditional Pass, or Fail.
For changes that pass, the CAB review takes seconds. The change manager sees a green "Pass" certification, confirms it is attached to the change record, and moves on. The pentest does not add meeting time for clean changes -- it simply adds confidence.
For changes that fail, the pentest saves the CAB significant time by surfacing security issues before they become incidents. A 15-minute discussion about whether to approve a change with two exploitable High severity findings is far less costly than a multi-day incident response after those vulnerabilities are exploited in production.
The net effect on change velocity is usually positive. Organizations that implement security certification report that the total time from change submission to production deployment decreases because the security gate catches issues early -- issues that would otherwise be discovered post-deployment and require emergency changes, rollbacks, or incident response. Catching a vulnerability in staging through automated pentesting takes days. Responding to the same vulnerability as a production security incident takes weeks.
The Governance Perspective
For IT governance professionals and change managers, security certification through automated pentesting addresses several persistent governance challenges.
Auditability. Every change in scope has a documented security test result. Auditors reviewing your change management process can see that security risk was objectively assessed for each change, not just self-reported by the change implementer. This is particularly valuable for SOC 2 Type II audits, where auditors examine change management controls (CC8.1) over the observation period.
Consistency. Human risk assessments are inherently inconsistent. Different developers rate similar changes differently. Different change managers apply different scrutiny levels. Automated pentesting applies the same testing methodology to every change, producing consistent, comparable results.
Accountability. When a change that introduced a vulnerability is traced back, the security certificate provides clear documentation of what was tested and what was known at the time of approval.
Compliance evidence. PCI DSS Requirement 6.3.2 requires that custom code changes are reviewed before release. ISO 27001 Annex A control A.8.32 addresses change management for information processing. NIST SP 800-53 control CM-4 requires security impact analysis for changes. Automated pentesting as part of change management provides direct evidence for all of these controls.
Organizations implementing security certification report that total time from change submission to production deployment decreases. Catching a vulnerability in staging through automated pentesting takes days. Responding to the same vulnerability as a production security incident takes weeks.
From Governance Theory to Operational Practice
The gap between change management governance theory and operational practice is wide in most organizations. Policies say that risk must be assessed. In practice, risk assessment is a dropdown menu on a form. Policies say that security must be considered. In practice, security review is a checkbox that gets checked by default.
Automated pentesting closes this gap by making the security assessment concrete, objective, and automatic. It does not require change managers to become security experts. It does not require developers to perform security testing on their own code. It does not require additional headcount or manual process steps. It runs in the background, produces a clear result, and integrates into the existing change workflow.
The organizations that implement this model find that their change management process becomes genuinely risk-aware rather than performatively risk-aware. Change managers make better decisions because they have better information. Developers get faster feedback on security issues because testing happens before production, not months later. Security teams gain visibility into the change pipeline without becoming a bottleneck.
This is what effective governance looks like: not more process, but better information flowing through existing processes.
Frequently Asked Questions
Should penetration testing be part of change management?
Yes. ITIL change management requires risk assessment before production changes, but most CABs lack objective security evidence. Automated pentesting provides a pass/fail security gate that change managers can require before approving releases, closing the gap between governance theory and practice.
How do you assess security risk before production changes?
Run automated penetration testing against the change in a staging environment before the CAB review. The pentest report provides objective evidence of exploitable vulnerabilities, giving change managers concrete data to approve, defer, or reject the change.
What is security certification for change management?
Security certification is a documented pentest result attached to a change request, proving the change was tested for exploitable vulnerabilities before production deployment. It functions like a quality gate — similar to how QA sign-off certifies functional correctness.
