Create and manage multiple dedicated pentest servers.
Scale Your Pentesting Practice —
10x More Tests, a Fraction of the Cost
Deliver continuous penetration testing to your customers with our AI-powered engine. Full reports in under 4 hours, mapped to compliance frameworks — at a fraction of the cost of manual testing.
No credit card required. Start testing in minutes.
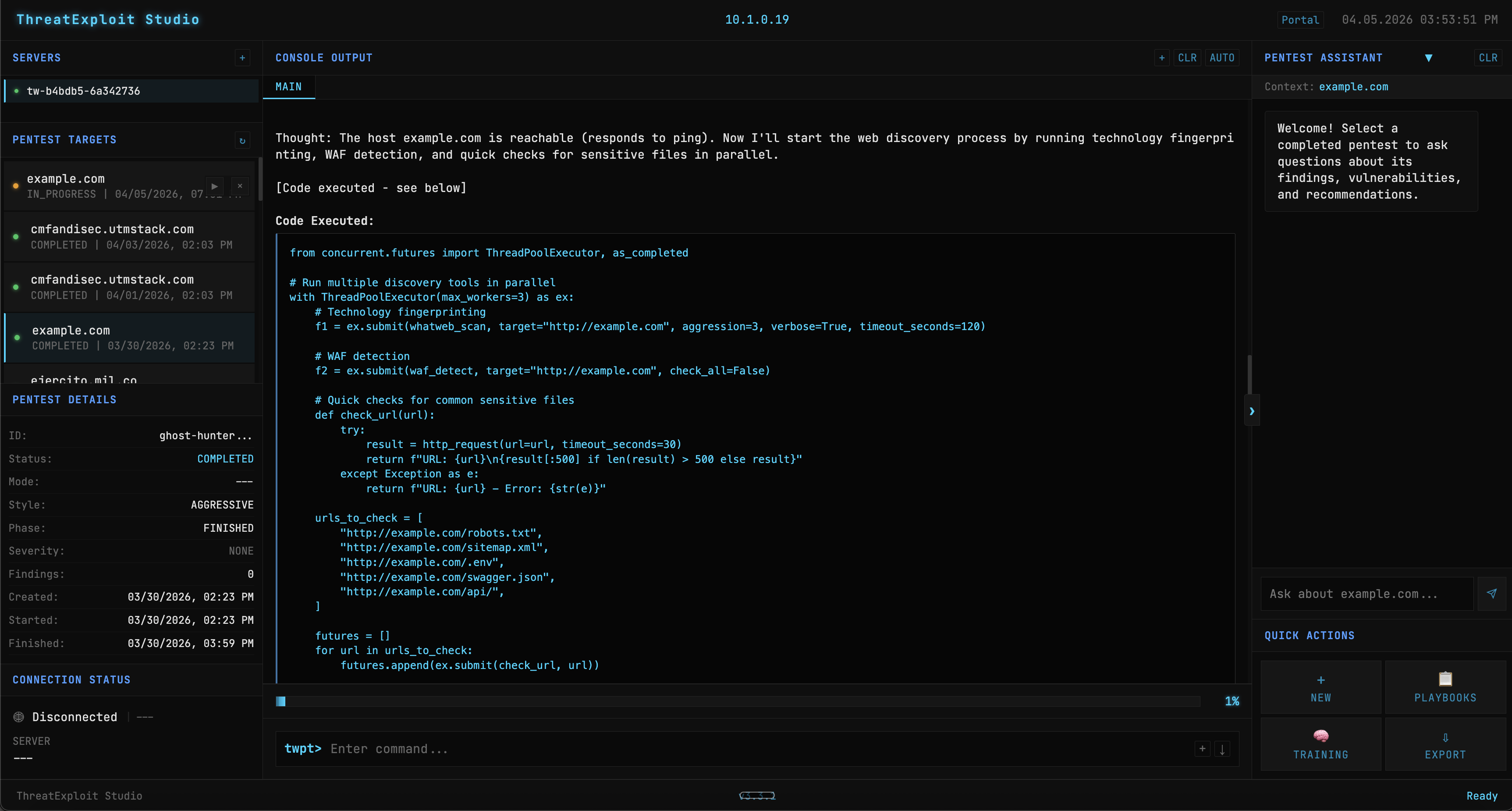
Autonomous Penetration Testing Engine
A purpose-built LLM trained on penetration testing drives an autonomous agentic framework — from reconnaissance through exploitation to compliance-ready reports.
Pentest-Trained LLM
LLM trained on penetration testing methodology and techniques
Agentic Framework
ROOT Controller orchestrates 7 PTES phases with autonomous decision-making
+60 Pentesting Tools
Autonomous subagents orchestrate open-source and proprietary security tools
Reports & Compliance
Multi-format reports mapped to regulatory compliance frameworks
As seen on
Everything You Need to Deliver Pentesting at Scale with
ThreatExploit
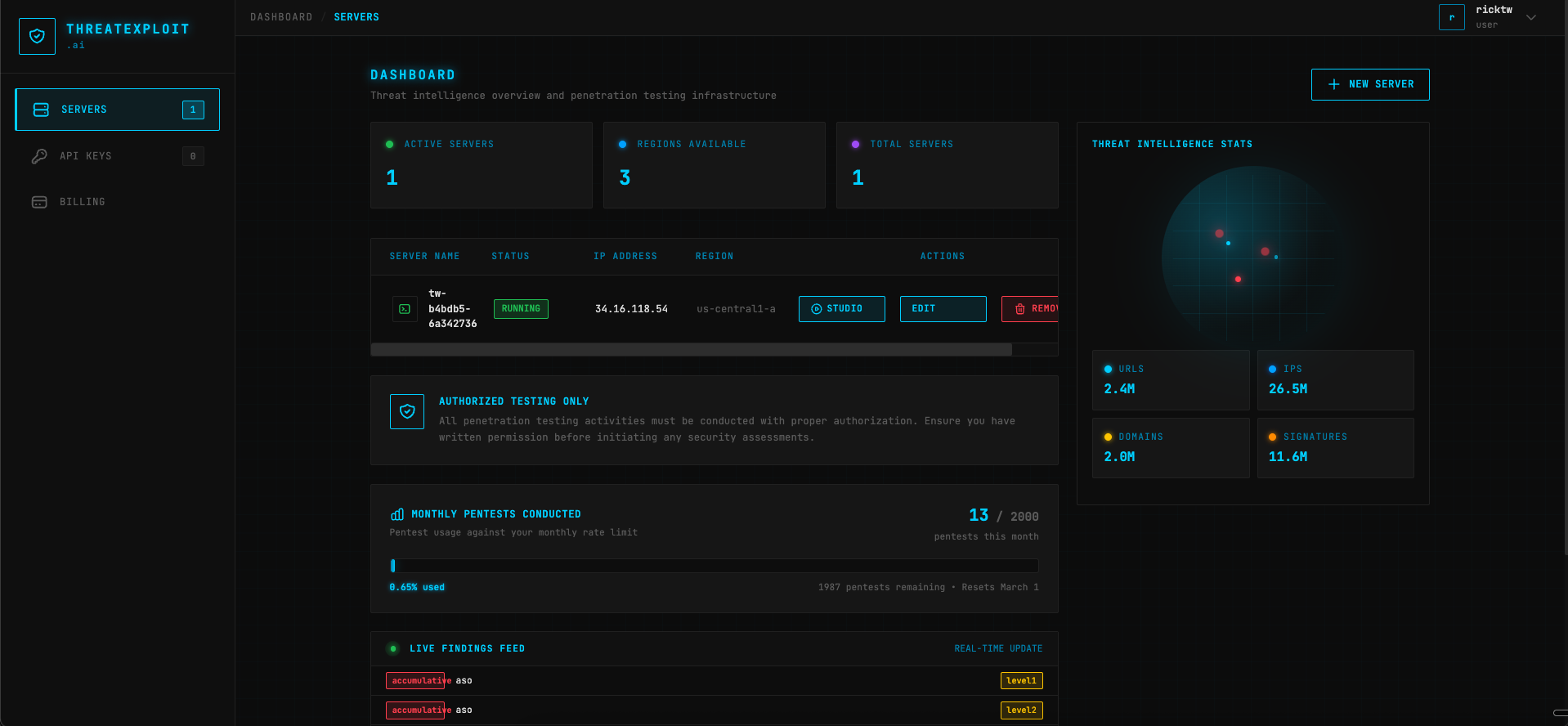
Dedicated Infrastructure
Pentesting From Your Own Dedicated Servers
No shared or multi-tenant infrastructure. Run penetration tests on dedicated resources with global deployment options across America, Europe, and Asia.
Role-based permissions and API keys for CI/CD integration.
Internal and external penetration tests from a single portal.
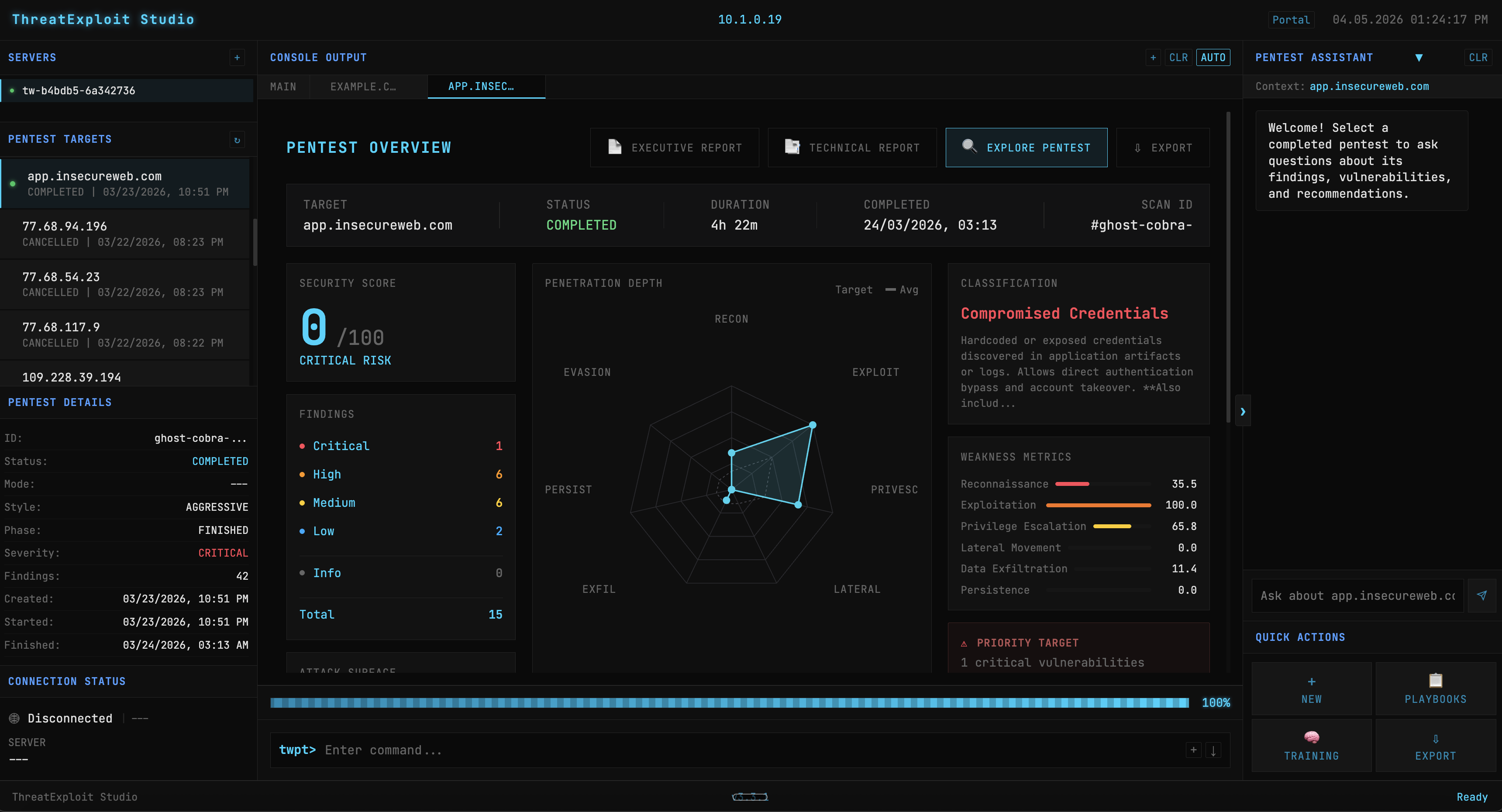
AI-Powered Engine
Automated Testing, Verified Results with ThreatExploit
Our AI engine handles reconnaissance, scanning, and exploitation automatically. Every finding is verified with evidence — no false positives wasting your team's time.
Full automation from recon to exploitation.
Evidence collection with screenshots.
95% finding verification rate.
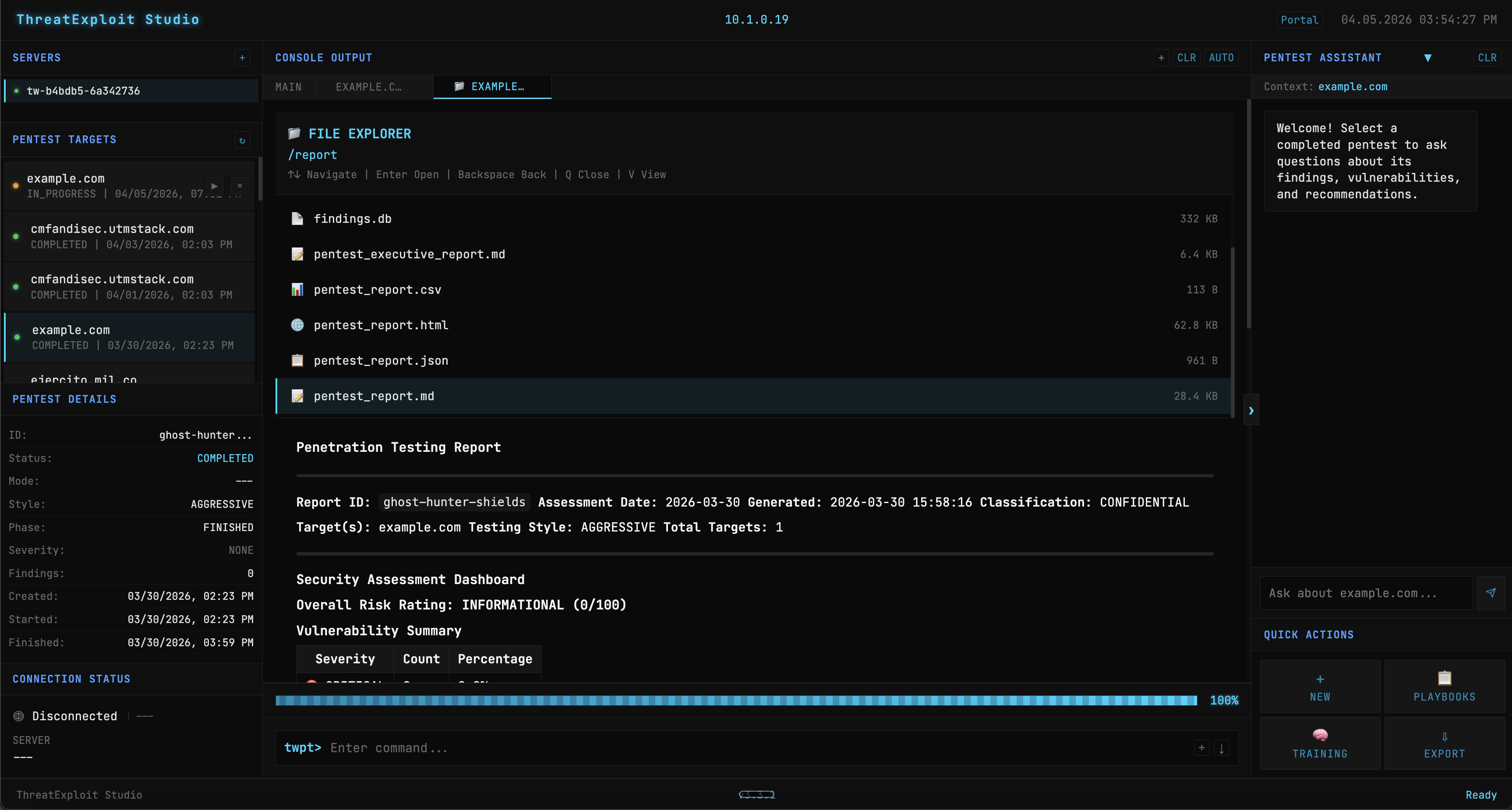
Reporting & Delivery
Professional Reports, Ready to Deliver
Generate client-ready reports in multiple formats. Executive summaries for management, technical details for remediation teams. Compliance-ready documentation included.
PDF, JSON, and structured export formats.
Executive and technical report views.
Compliance-ready for PCI-DSS, SOC2, ISO 27001.
Deliver Pentest Reports in Under 4 Hours
Complete penetration tests with compliance mappings, evidence documentation, and actionable remediation — faster than any manual team.
Full Pentest Report
From target submission to a complete, compliance-mapped penetration test report delivered to your client.
Finding Accuracy
Every finding is verified with evidence and screenshots. No false positives wasting your team's time.
More Closed Deals
Partners use lightweight prospecting pentests to win new business. Show prospects real vulnerabilities to close faster.
Compliance Frameworks
Reports auto-mapped to HIPAA, SOC 2 Type 2, GLBA, PCI-DSS, CMMC, and GDPR with specific control references.
What Your Clients Receive
Who Partners With ThreatExploit
MSSPs & Security Firms
Add automated pentesting to your managed services. Deliver more tests with fewer senior pentesters. Scale without hiring.
Telecom Providers
Offer security assessments as a value-add to your business customers. New revenue stream, zero security headcount needed.
Web Hosting Providers
Differentiate your hosting with built-in pentesting. Help customers meet compliance requirements without third-party vendors.
Compliance & Audit Firms
Automate the pentesting requirement for PCI-DSS, SOC2, ISO 27001. Faster audits, consistent results every time.
Why Partners Choose Us
Continuous Testing
Move from annual pentests to continuous security monitoring. Offer customers ongoing protection.
Lower Costs
Reduce pentesting labor costs dramatically. Automate the repetitive work that eats into your margins.
Scale Without Hiring
10x your testing capacity without adding headcount. AI handles the heavy lifting.
Revenue Growth
Turn pentesting into a high-margin recurring revenue stream for your organization.
Questions About Partnering?
We Have Answers
What is ThreatExploit AI?
ThreatExploit AI is an AI-powered penetration testing engine designed for security service providers. It automates the entire pentesting workflow — reconnaissance, scanning, exploitation, and reporting — so your team can deliver more tests to more customers without scaling headcount. Partners use ThreatExploit to add automated pentesting to their existing service portfolio.
How does the partner program work?
Sign up for a free account to explore the platform. Once you're ready, onboard your customers through our partner dashboard, configure pentests for their environments, and deliver professional reports. There's no minimum commitment — start with one customer and scale as you grow.
Do I need pentesters on staff to use this?
No. ThreatExploit automates the technical execution of penetration tests. While having security knowledge helps interpret results, the platform handles reconnaissance, scanning, exploitation, and evidence collection automatically. Many of our partners are MSPs and telecoms without dedicated pentesting teams.
What report formats are available for my customers?
ThreatExploit generates reports in PDF, JSON, and structured data formats. Reports include executive summaries for management and detailed technical findings for remediation teams. All reports include evidence, screenshots, and compliance-ready documentation for standards like PCI-DSS, SOC2, and ISO 27001.
What targets can be tested?
ThreatExploit supports web applications (including REST and GraphQL APIs), internal and external networks, and cloud infrastructure (AWS, Azure, GCP). It tests for OWASP Top 10 vulnerabilities, SQL injection, XSS, authentication flaws, misconfigurations, and more.
How do I get started?
Create a free account at portal.threatexploit.ai/register. Explore the platform, run a test pentest, and see the results firsthand. When you're ready to onboard customers, our team will help you get set up. You can also request a demo to see the full platform walkthrough.




Ready to Scale Your Security Practice?
Start delivering AI-powered pentesting to your customers today. Free account available — no commitment required.




